Cybersecurity for Connected Medical Devices: IEC 81001-5-1, Regulations, Standards, and Technologies in 2026
How Manufacturers Can Meet Regulatory Requirements and Defend Against Cyber Threats
As medical devices become increasingly connected, cybersecurity is critical to protect patient safety and sensitive health data. It is estimated that one in four medical devices is already connected to the Internet or a hospital network. In 2017, their total number was an estimated 337 million, with an expected compound annual growth rate (CAGR) of 20.8% through 2030, including digital health apps, whose development is being driven by the German Digital Healthcare Act (DVG) and similar initiatives across Europe [1].
Digital health apps are increasingly part of health care. Approximately 200 health apps are added to the app stores daily [2]. Any connected medical device or Internet of Medical Things (IoMT) product is a potential target for cyberattacks that can compromise patient or user safety or leak highly sensitive healthcare data. The rapid growth of the Internet of Medical Things (IoMT) and digital health apps has heightened the risk of cyberattacks.
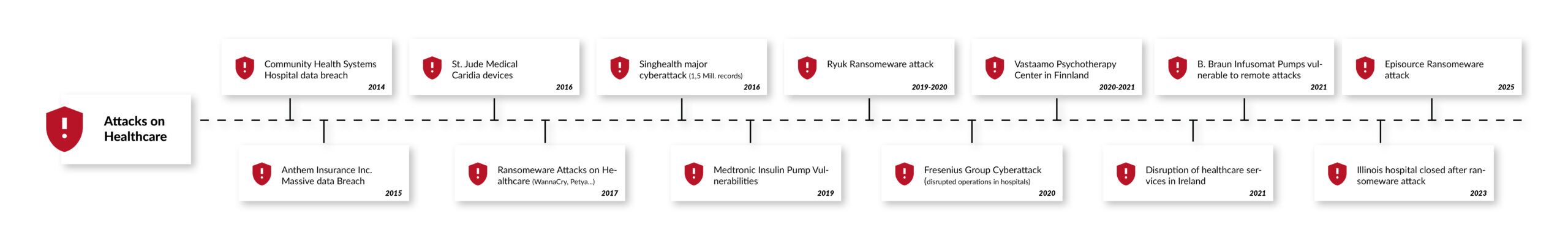
In a recent survey, four out of five medical device manufacturers stated that they had been targeted by at least one cyberattack in 2019 [3]. Other, more recent reports suggest an even darker picture. According to the "2021 Global Threat Intelligence Report" of the technology service company NTT, the number of cybersecurity incidents in the healthcare sector tripled in 2020 compared to the previous year.
Apart from health risks and high penalties for possible data protection breaches, successful cyberattacks or security vulnerabilities that become public can also damage the reputation of manufacturers. The German Federal Institute for Drugs and Medical Devices (BfArM), the U.S. National Cybersecurity and Communications Integration Center (NCCIC), and the U.S. Food and Drug Administration (FDA), for example, provide detailed information about known security risks in medical devices and name the product as well as the manufacturer [4]. Once lost, reputation and trust are difficult to regain, particularly in highly sensitive areas such as healthcare.
This white paper reflects the latest regulatory changes, standards, and technological advancements in medical cybersecurity as of 2025.
Regulatory Landscape
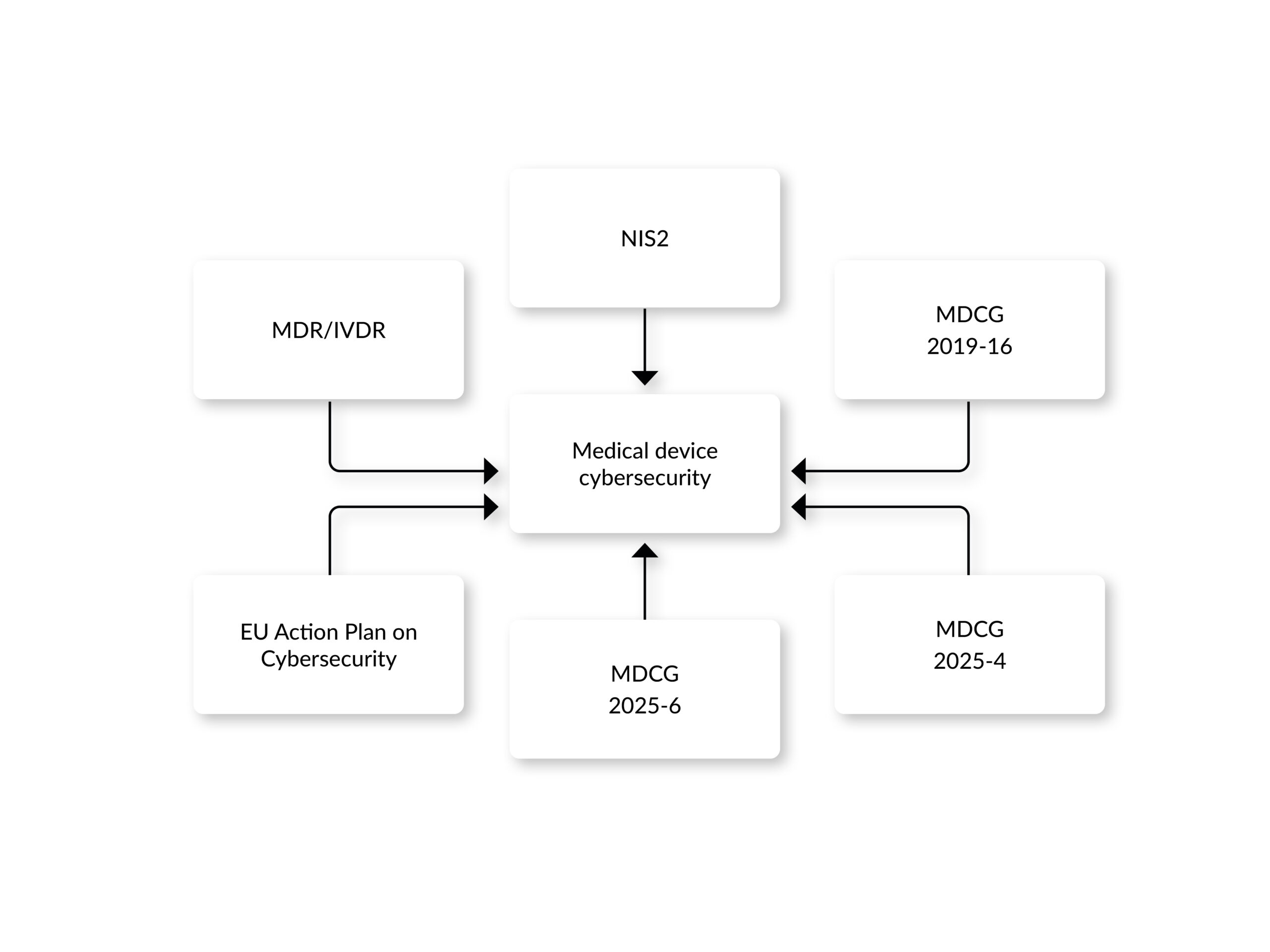
The regulatory environment for medical device cybersecurity has evolved significantly, with both the United States and the European Union introducing updated frameworks to address emerging threats.
European Union Regulations
Regulation (EU) 2017/745, also known as the Medical Device Regulation (MDR), forms the legal framework for all actors on the medical device market. Unlike the previous directives, it defines several explicit cybersecurity requirements. In particular, Annex I §§ 17.2 and 17.4 require development "according to the state of the art" with consideration of IT security, and the definition of security measures to protect against unauthorized access.
The guidance document MDCG 2019-16 specifies the implementation of a cybersecurity risk management process. It promotes a security-by-design and security-by-default approach and requires cybersecurity to be considered at every stage of the product lifecycle, from conception to post-market surveillance. Requirements explicitly named in the guidance include post-market surveillance, incident response, and a procedure for problem resolution.
NIS-2 Directive (EU) 2022/2555: In force since January 2023, NIS-2 does not specifically target medical devices but applies to organizations operating networks or systems connected to medical devices if they qualify as essential or important entities. It mandates risk management measures, incident reporting, and supply-chain security. In Germany, the NIS-2 Implementation Act (NIS2UmsuCG) entered into force in December 2025, establishing concrete obligations for affected manufacturers (thresholds: ≥ 50 employees or ≥ 10 M€ turnover).
MDCG 2025-4 and 2025-6: Two guidance documents published in June 2025. 2025-4 addresses the secure distribution of Medical Device Software (MDSW) on online platforms under MDR, IVDR and DSA. 2025-6 clarifies the interplay between MDR, IVDR and the EU AI Act, emphasizing cybersecurity for AI-enabled devices.
EU Action Plan on Cybersecurity (January 2025): The European Commission launched a plan to strengthen cybersecurity across hospitals and healthcare providers, including connected medical devices, via a pan-European cybersecurity support center.
- NIS2 Directive (EU) 2022/2555: Effective since January 2023, this directive does not specifically target medical devices; however, it can apply to the organizations that operate or manage networks or systems related to medical devices, if they are considered essential or important entities. For instance, it mandates risk management measures and incident reporting to enhance network and information system security across the EU.
- MDCG 2025-4: Published in June 2025, this guidance outlines requirements for safely distributing medical device software (MDSW) apps on online platforms, clarifying roles for app platform providers under the MDR, IVDR, and Digital Services Act (DSA). The guidance requires the specification of requirements for cybersecurity in medical device software.
- MDCG 2025-6: Released in June 2025, this FAQ-style document addresses the interplay between the MDR, IVDR, and the Artificial Intelligence Act, and among others, emphasizing cybersecurity considerations for AI-enabled devices.
- EU Action Plan on Cybersecurity: Launched in January 2025, the European Commission launched a plan aimed at improving the cybersecurity of hospitals and healthcare providers, including connected medical devices, by establishing a pan-European Cybersecurity Support Centre.
United States Regulations
In the U.S., the Food and Drug Administration (FDA) has significantly updated its cybersecurity oversight in recent years:
- FDA Final Guidance „Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions“ (Final, June 2025): Updates the 2023 guidance to align with new statutory requirements for "cyber devices" under Section 524B FFDCA. Highlights include a mandatory Software Bill of Materials (SBOM) in SPDX or CycloneDX format with the NTIA seven minimum elements, explicit Secure Product Development Framework (SPDF) activities (threat modeling, secure coding, encryption/authentication, robust software testing), and a 12-document eSTAR submission package covering everything from threat modeling to vulnerability communication.
- Section 524B FFDCA: Added in December 2022 under Section 3305 „Ensuring Cybersecurity of Devices“, this law requires every premarket submission (510(k), De Novo, PMA) for a cyber device to demonstrate cybersecurity. With the 2025 final guidance in place, cybersecurity compliance has shifted from voluntary recommendation to enforceable legal obligation.
- Although FDA guidance focuses on U.S. submissions, its practical content (SPDF, SBOM, post-market vulnerability management) is highly recommended reading for any manufacturer — the underlying concepts align with EN IEC 81001-5-1 and complement it.
- The FDA guidance “Cybersecurity in Medical Devices: Quality System Considerations and Content of Premarket Submissions” was updated in 2025 with clarifications on the term „cyber device“ and contains recommendations on device design, labeling, and documentation for premarket submissions, including requirements for a Software Bill of Materials (SBOM) and post-market vulnerability management plans. The FDA’s guidance emphasizes a Secure Product Development Framework (SPDF) to reduce vulnerabilities throughout the device lifecycle, aligning with global best practices. Despite being a US FDA guidance and focusing on compliance with FDA requirements, it’s a highly recommended literature for a pragmatic and at the same time effective implementation of cybersecurity in a medical device, even for those not targeting the US market.
- Section 524B of the FD&C Act: This law was updated by the omnibus bill, which was signed into law in December 2022, and added section 3305 with „Ensuring cybersecurity of devices“. The content of the law is surprisingly clear, as it requires, basically, for all submissions, such as 510(k) information, that proves the device is cyber secure.
How We Support Your Compliance Journey
Navigating EU and FDA cybersecurity rules is complex. We provide gap analyses against MDR, NIS-2 and FDA requirements and define clear roadmaps to conformity. Our team supports 510(k), De Novo and PMA submissions with SBOMs, risk files and post-market surveillance plans — or delivers a final report with findings, strategies and recommendations for long-term compliance across the entire lifecycle of your medical devices.
Standards and Guidelines
Standards play a crucial role in ensuring harmonized cybersecurity practices across the medical device industry, providing the presumption of conformity under MDR and IVDR.
What does IEC 81001-5-1 regulate?
The full title of IEC 81001-5-1:2021 is "Health software and health IT systems safety, effectiveness and security – Part 5-1: Security – Activities in the product life cycle". Published in December 2021 and followed by the EU-harmonised version EN IEC 81001-5-1:2022, the standard defines lifecycle requirements for secure development and maintenance of health software. In 2025, the official Interpretation Sheet (IEC 81001-5-1:2021/ISH1:2025) was published, clarifying specific requirements.
The standard is process-oriented: it does not prescribe specific technical solutions but requires a structured security process in the Quality Management System. It supplements the software lifecycle of IEC 62304 with security activities at the respective phases and integrates with the risk management framework of ISO 14971. It is structurally derived from IEC 62443-4-1 and adapted to the specific needs of health software.
IEC 81001-5-2 (Draft): A complementary standard focused on Security Risk Management for manufacturers is in draft (based on AAMI SW96). Once published, it will be applied jointly with IEC 81001-5-1. Until then, AAMI SW96 serves as the reference for detailed security risk management processes.
Related Standards
- ISO 14971:2019 (+ Amd. 2024): Fundamental risk management standard for medical devices, updated to include data and cybersecurity risks. Security risks are managed within the overall risk management process, not separately.
- IEC 62304: Software lifecycle for medical device software — IEC 81001-5-1 is designed to supplement this process with security activities.
- ISO/IEC 27001:2022 & 27002:2022: Information security management — provides organizational context; specific controls can be adopted into the IEC 81001-5-1 security process.
- IEC TS 81001-2-2:2025: Technical specification for communicating security needs, risks and controls between manufacturer and operator — complements the MDS2 format.
- IEC/TR 60601-4-5:2021: Technical report on secure design practices for active medical devices with network components.
Compliance Checklist: What IEC 81001-5-1 Actually Requires
The following checklist summarises the key activities manufacturers must anchor in their development and maintenance processes. It does not replace a full gap analysis but supports a first self-assessment:
- Security Process in QMS: Documented security lifecycle as extension of IEC 62304 software lifecycle, anchored in the ISO 13485 QMS.
- Security Requirements: Documented security requirements derived from threat modeling and threat analysis of the intended clinical environment.
- Threat Modeling: Systematic identification of threats and attack vectors (e.g. STRIDE methodology), referenced to the intended use of the medical device.
- Security Risk Assessment: Integrated with ISO 14971 risk management — security risks feed into overall risk management, not a separate track.
- Secure Software Development: Secure coding standards, code review, static analysis (SAST), dependency management, no known-vulnerable open-source components.
- Verification & Validation: Security testing as an independent V&V activity (penetration tests, fuzz testing, vulnerability scans).
- Secure Release Management: Software Bill of Materials (SBOM) in SPDX/CycloneDX format, signed releases, secure update mechanisms.
- Post-Market Security: Continuous vulnerability monitoring (CVE feeds, CNA information), defined incident response process, timely security patches.
- Communication & Documentation: Accompanying documentation for operators (MDS2 form or equivalent), security information in the instructions for use.
- Legacy Devices: Assessment of existing products, gap analysis against IEC 81001-5-1, retrofitting of required process and documentation elements.
Advancements in Cybersecurity Technologies
Technological advancements are shaping the future of medical device cybersecurity, offering both opportunities and challenges:
Artificial Intelligence (AI)
AI is increasingly integrated into medical devices (e.g., for diagnostic purposes) and at the same time used in separate systems to safeguard medical devices through cybersecurity tools, for instance, to protect networks and data flows connected to devices.
AI can analyze device behavior, network traffic to identify unusual patterns that may indicate cyberattacks, hence providing anomaly monitoring and threat detection. AI Models can also predict and anticipate potential security weaknesses. By processing historical data and threat intelligence, it recommends proactive measures, like patching or isolating at-risk devices, before exploits occur. Additionally, AI systems can be designed to identify and counter sophisticated attacks, such as social engineering or source code extraction, by learning from patterns and adapting defenses dynamically.
However, while AI offers improved clinical performance and protective benefits, its integration into medical devices introduces new vulnerabilities. AI models are complex, often opaque, and reliant on a vast amount of data, making them targets for attackers. This can expand the attack surface, leading to risks that compromise patient safety, data integrity, and system reliability. Attackers can, for instance, exploit AI through techniques like data poisoning (altering training data to degrade performance) or evasion attacks (crafting inputs to fool the model). For example, experiments have shown that dataset poisoning can reduce ML model accuracy by up to 24%, leading to incorrect diagnoses or treatments in devices like imaging systems [5].
Secure Product Development Framework (SPDF)
Recommended as a key requirement by the FDA, the SPDF is defined as "a set of processes that help identify and reduce the number and severity of vulnerabilities in products". It focuses on security risk management, architecture design, and testing to reduce vulnerabilities and encompasses the entire product lifecycle, including design, development, release, support, and decommissioning.
The framework aims to ensure that medical devices are designed securely and can mitigate emerging cybersecurity risks. Key elements are Security Risk Management, Threat Modeling and Vulnerability Assessment, Secure Design and Development Practices, Testing and Validation, Post-Market Monitoring and Maintenance, and Documentation and Transparency. The FDA's SPDF closely correlates with IEC 81001-5-1, as the FDA guidance explicitly references the standard as an example of a framework that can help implement SPDF processes. Both emphasize a lifecycle approach to cybersecurity, integrating security into design, development, and maintenance and ensuring ongoing risk mitigation.
Microsegmentation
This cybersecurity technique creates isolated network segments to improve the security of medical devices. Microsegmentation can significantly strengthen the cybersecurity of medical devices by reducing the ability of attackers to move freely through a hospital network once they gain access to a vulnerable device. Microsegmentation enhances medical device cybersecurity by dividing networks into smaller, isolated segments, limiting the spread of cyberattacks. In a hospital network, if one device or system is compromised, microsegmentation prevents attackers from moving laterally to other devices.
It’s particularly effective for protecting legacy devices. Legacy devices often run outdated operating systems, can’t be easily patched (for instance due to regulatory constraints), and may use insecure protocols. Microsegmentation addresses these risks by reducing the network “blast radius” if a breach occurs. IEC 81001-5-1, FDA premarket guidance, and NIS2 encourage least-privilege network design, microsegmentation is one solution to implement such a design.
Frequently Asked Questions About IEC 81001-5-1
Conclusion
In the development of connected medical devices, software-driven medical devices, or stand-alone medical software, cybersecurity must be considered from the very early stages of the development. This is necessary, required, and mandatory for market access in Europe, the USA, and all other key markets. At the same time, cybersecurity is a dynamic field requiring constant vigilance and adaptation. The updated regulatory frameworks, standards like IEC 81001-5-1, and technological advancements provide manufacturers with tools to enhance device security.
However, recent incidents like the McLaren Health Care cyberattack highlight the persistent threat landscape. By integrating cybersecurity from the early beginning of the development and design to decommissioning, adopting best practices, and staying informed about regulatory changes, manufacturers can protect patients, maintain trust, and ensure compliance in an increasingly connected healthcare ecosystem.
References:
[1] IHS Markit, The Internet of Things: a movement, not a market, e-paper, downloaded 06/14/2021: https://cdn.ihs.com/www/pdf/IoT_ebook.pdf
[2] IQVIA Institute for Human Data Science: The Growing Value of Digital Health, accessed 06/21/2021: https://www.iqvia.com/insights/the-iqvia-institute/reports/the-growing-value-of-digital-health
[3] Irdeto, Global Connected Industries Cybersecurity Survey. IoT Cyberattacks Are The Norm – The Security Mindset Isn’t, downloaded 06/14/2021: https://go.irdeto.com/connected-industries-cybersecurity-survey-report/
[4] Bundesinstitut für Arzneimittel und Medizinprodukte, Cybersicherheit von Medizinprodukten, accessed 06/14/2021: https://www.bfarm.de/DE/Medizinprodukte/RisikoerfassungUndBewertung/Cybersicherheit/kundeninfos_cybersicherheit_node.html
[5] Research Handbook on Health, AI and the Law. Chapter 4Cybersecurity of AI medical devices: risks, legislation, and challenges. https://www.ncbi.nlm.nih.gov/books/NBK613217/
[6] Cybersecurity requirements for medical devices in the EU and US - A comparison and gap analysis of the MDCG 2019–16 and FDA premarket cybersecurity guidance, “Computational and Structural Biotechnology Journal”, Volume 28P259-2662025
[7| “A Way Forward for the MDCG 2019-16 Medical Device Security Guidance”, https://doi.org/10.1145/3652037.3663894